SET SEG: Not Your Typical Insurance Company

For most insurance companies, success is defined by profit and financial benchmarks. But for SET SEG, that’s not the case — we’re not an insurance company. Our members join a pool and fund as opposed to going with a traditional insurance carrier, meaning member districts are our shareholders and have a voice in our strategic direction. The success of the Pool and Fund allows members to receive net asset returns and premium reductions.
Insuring public schools is a risky endeavor, and in Michigan, where the summers are short and the winters are freezing, providing affordable and quality coverage on everything from property/casualty and workers’ compensation to employee benefits, can be a challenge.
As our schools face these challenges, we like to remind them one thing: they’re not alone.
From our corporate programs and workplace culture to our philanthropic efforts through the SET SEG Foundation, giving back to our schools and communities has become a part of the SET SEG approach, always connecting back to our core value to put schools first.
12 Ways SET SEG Gives Back
12. Property/Casualty Return Checks
Every year, districts that are members of the MASB/SEG Property/Casualty Pool receive a net asset return check for funds not utilized in covering claims the previous year. As members of the Pool, school districts share the risk but benefit when claims are reduced and prevented.

11. Workers’ Compensation: Funding Safety Initiatives
Every spring, the SEG Self-Insurer Workers’ Compensation Fund sends a check to each member of the Fund so those districts can purchase products that will help decrease common injuries that occur inside the classroom, with the ultimate goal of reducing injuries and claims across the state.

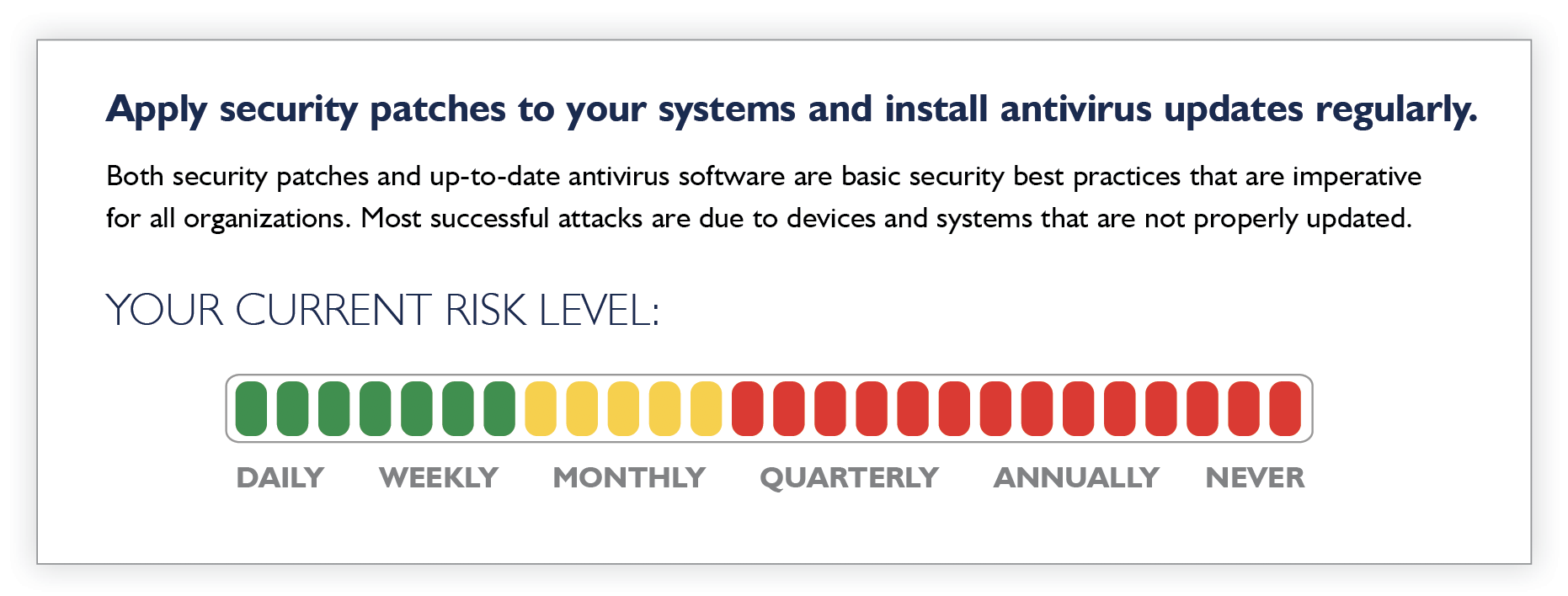
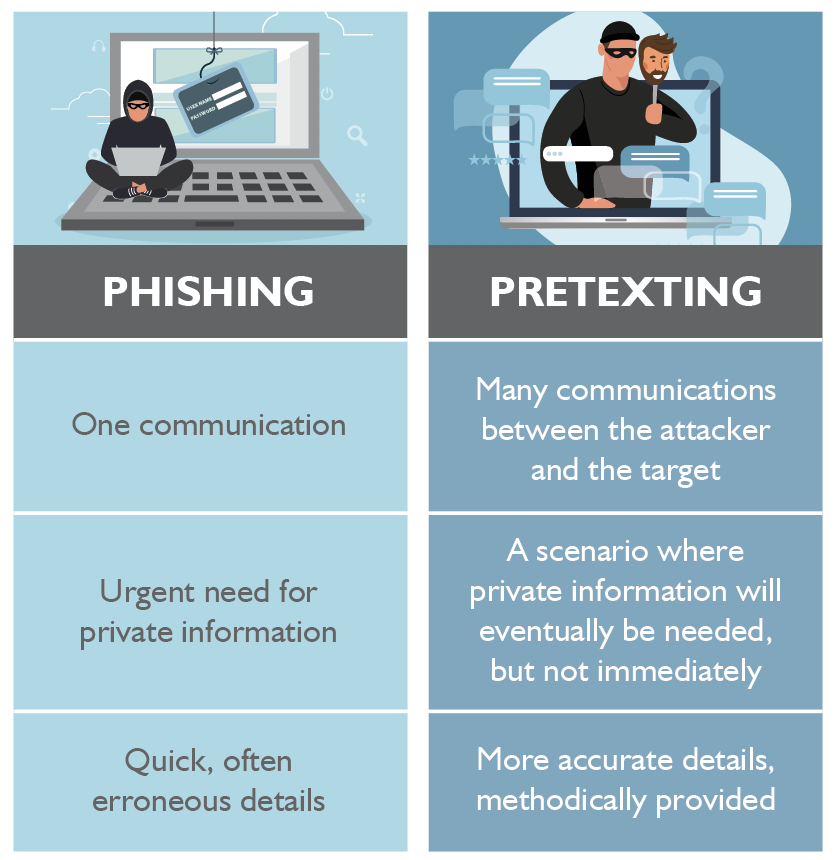
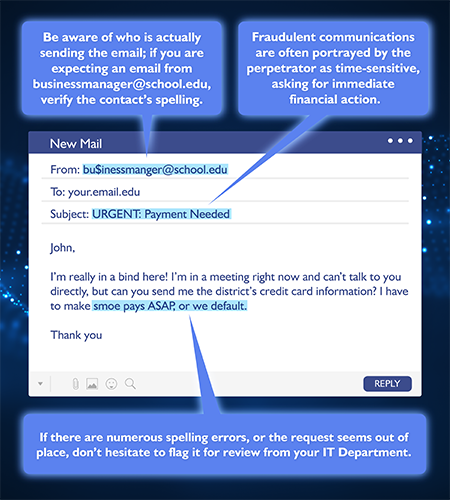
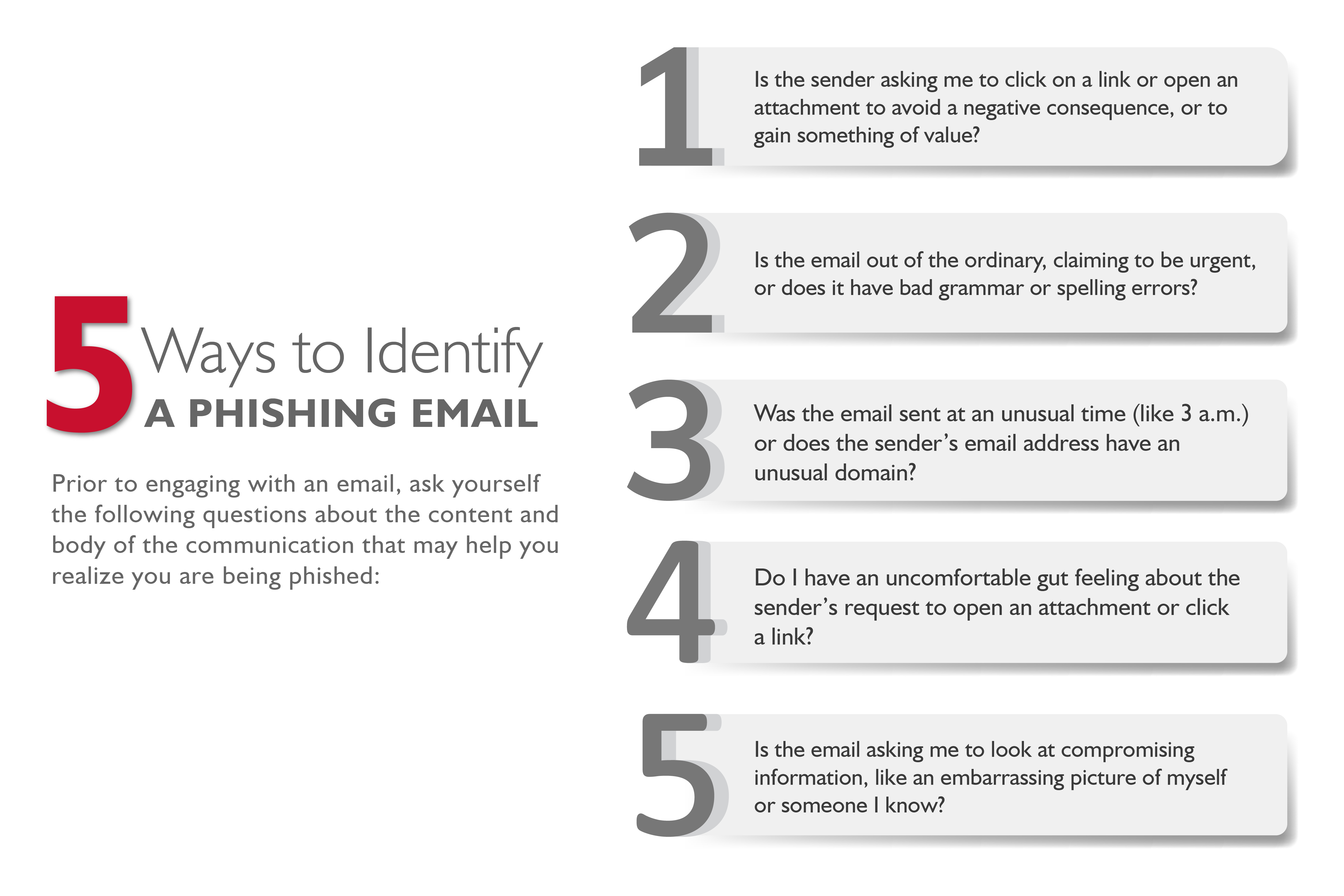
10. Free Subscription to MyCyber
It’s not enough to provide funds for the property and buildings our students and educators populate, protecting districts from cyber threats is also a top priority. Through a partnership with Tetra Defense, a leading cybersecurity firm, SET SEG provides a valuable tool for members to scan their systems allowing schools to shore up their cyber defenses, keeping their school community safe from damaging cyber incidents.
SET SEG is providing all members with a free subscription to MyCyber, a platform used to conduct cyber hygiene projects ensuring schools are following cyber security best practices and have all the tools they need to remain secure. Click to learn more.

9. Adopt a Family
As an organization, participating in Adopt-a-Family prior to the holidays is a great way to engage our employees and give back to the community at the same time. Each year, SET SEG pledges to assist one or two families who may be struggling to provide gifts for their children.
This season, our staff is purchasing and donating enough gifts to cover a family of five.

8. Employee Food Drive
For two weeks this November, our staff brought in food donations to the office for a food drive benefitting the SIREN/Eaton Shelter in Charlotte, Michigan, a community resource dedicated to providing advocacy and support services to the homeless population and domestic violence survivors.

7. Paid Volunteer Time
While giving back is top of mind during the holiday season, SET SEG has put in place policies that encourage philanthropy all year round, specifically through paid volunteer time and donating to our Foundation with payroll contributions. Employees are given eight hours of paid time off from work to volunteer for a cause, event, organization, etc. of their choice.
In addition to giving their time, many SET SEG employees take advantage of our payroll contribution option to donate an amount per day period to the SET SEG Foundation, directly donating to grant and scholarship programs benefiting our public schools.

6. Send a Candy Cane
In December, as a fundraiser for the SET SEG Foundation, the philanthropic arm of our organization, staff can pay $1 to send a coworker a festive treat with a message to share their appreciation during the holiday season.
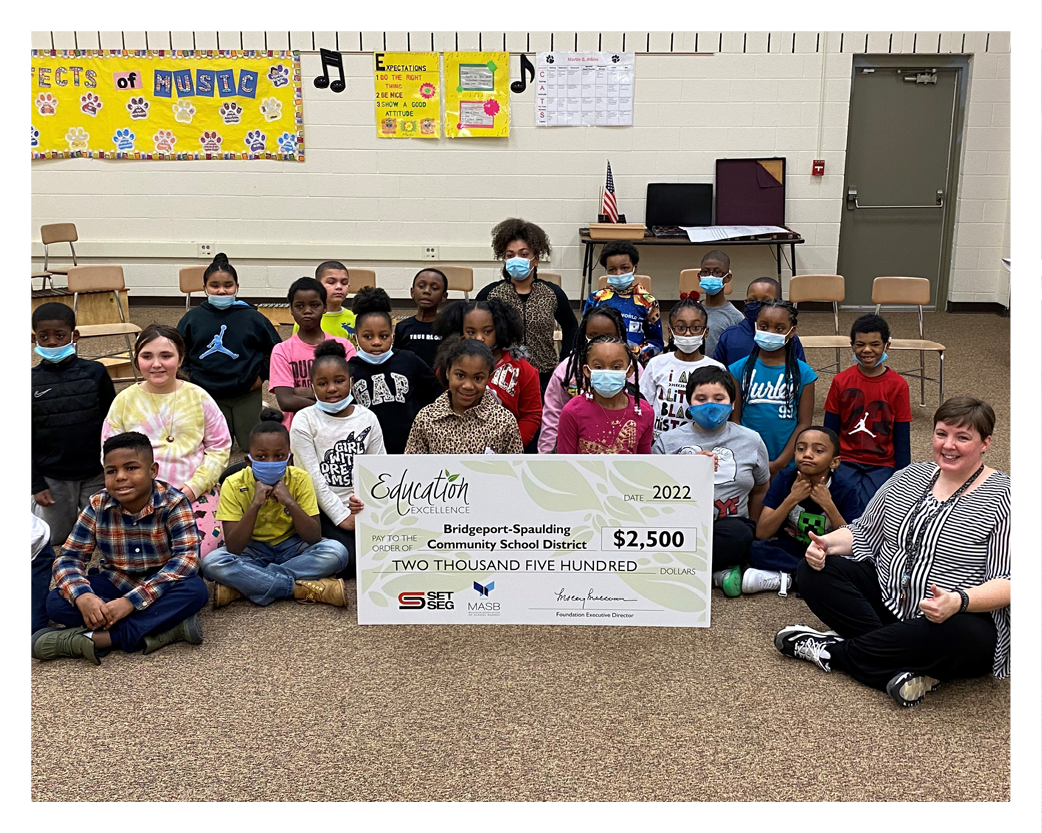
5. Award 10 Schools $2,500
The SET SEG Foundation is once again partnering with the Michigan Association of School Boards to honor Michigan public school programs with Education Excellence Awards. Ten educational programs within Michigan public schools and/or ISDs will be awarded the grant to continue their positive influence on their students and community.
Winners receive $2,500, a commemorative trophy, and a street sign announcing the districts as an Education Excellence winner. Apply here: setseg.org/edex

4. Send 65 Students to Summer Leadership Camp
The Michigan Association of Student Councils and Honor Societies (MASC/MAHS) Summer Leadership Camp provides an opportunity for students to experience lessons in leadership, communications, group activities, and goal setting. Through this competitive process, students in grades nine through 12 receive scholarships to attend camp.
Every year, SET SEG receives hundreds of applications from all throughout Michigan and awards $26,000 in full scholarships. Click to learn more.

3. Provide 20 Students Scholarships for the Skilled Trades
The SET SEG Foundation believes in supporting Michigan public school students in the pursuit of enrichment opportunities that advance learning and create opportunities. With the shortage of skilled trade workers in Michigan, we want to help revitalize these career paths and support students in their professional pursuits by giving 20 scholarships each in the amount of $500. Click to learn more.

2. Award 3 School Districts in the Student Showcase
Each year MASC/MAHS invite students across the state to develop a student showcase presentation that shares the very best in programming currently being executed at their school. Presentations are held at regional events throughout the state and can be selected to present at the state conference in February. The top presentations are voted on by attending schools for a chance to present to more than 2,000 student leaders from across the State of Michigan. Students attending the state conference will vote for the top three winners.
The SET SEG Foundation awards the top three winning school districts $1,000.

#GivingTuesday: SET SEG Foundation
Throughout our #12WaysOfGiving series we’ve covered all the ways SET SEG gives back to Michigan’s schools and communities, even highlighting our generous staff for all they give throughout the year in addition to their hard work serving our members every day.
Now it’s your turn.
If you would like to contribute to any of the SET SEG Foundation’s programs benefitting Michigan public school educators and students, please donate today: setseg.org/donate.