The Costliest Form of Cybercrime

Have you ever received a suspicious email from a contact you trust? Maybe it’s from a local print shop asking for immediate payment on an invoice for flyers for your district. It could be from your business manager requiring sign off on gift cards to employees. It could even be from a third-party contractor or district administrator asking for payment information to take care of construction costs.
Unfortunately, while those communications may appear innocent on the surface, the thing they all have in common is that none of them are actually from a trusted contact. Business email compromise (BEC) occurs when bad actors portray themselves as trusted parties. While not necessarily as prevalent as ransomware attacks, this form of cybercrime is the most financially costly to organizations, and one that has become increasingly common in K-12 institutions.
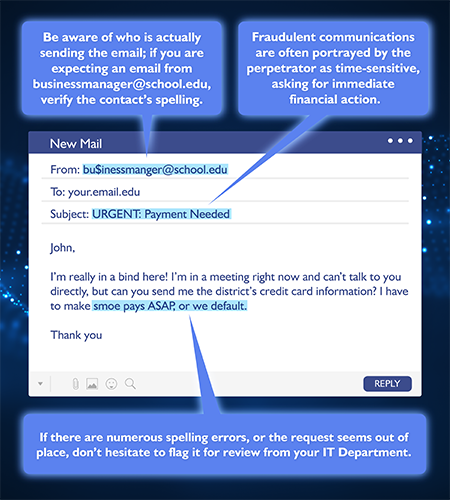
These fraudulent communications are often portrayed by the perpetrator as time-sensitive, asking for immediate financial action before the reader can accurately assess the validity of the request. While the short timeframe is part of what can make attacks successful, it’s also their downfall.
Taking time to scrutinize the email is all it takes to prevent a costly mistake.
Documents and videos in the SET SEG Cyber Security Resource Center describe, in detail, the dangers of phishing attacks from cybercriminals trying to steal your data and how to mitigate them. BEC threats follow some of the same rules.
Business email compromise attacks can be a costly hazard but taking the steps to educate employees on cyber security best practices is the key to protecting your district.
- Participate in regular phishing training, like KnowBe4’s cyber awareness training.
- Put strict policies in place, only allowing the use of district-managed devices for work-related tasks.
While cyberattacks are only becoming more common, SET SEG is committed to providing members with the greatest defense against such threats: knowledge.
If you haven’t already, visit our Cyber Security Resource Center to prepare your staff for whatever cyberthreats may come your way.